What happens when a company shifts from defense to offense, changes its posture, and sharpens its language?.
We know this because Microsoft spent years saying it had nothing against Linux. Then it started showing up at government procurement meetings with security briefings about why open-source software was a risk to national infrastructure. Google told publishers for a decade that it was just organising information. Then it started funding research that found journalism paywalls were bad for democracy. What used to be “we built something different” becomes “what they’re building is dangerous.” And if you are good enough at it and you have the right relationships, you do not even have to win the technical argument. Just make sure the technical argument gets decided by people who trust you more than they trust your competitors.
Canton is doing that now. And the crypto industry, for the most part, is missing from the conversation.
In January, I wrote that Canton chose efficiency over freedom and that institutions chose Canton. The framing was that Canton and Ethereum were solving different problems for different audiences. That framing was right at the time. Since then, Canton has moved.
Read: Wall Street’s Stealth Chain - by Thejaswini M A
Canton’s founders have been making the case to buyers and regulators, both publicly and in closed-door meetings, that zero-knowledge proofs (ZKPs) pose unacceptable risks for mission-critical financial systems. I think it’s a regulatory positioning campaign, which runs alongside a fundraising effort that brought in major players like Goldman Sachs, Citadel, DRW, Circle, Paxos, and Polychain. JPM Coin went live on Canton in January. Visa joined as a super validator in March. On March 27, LayerZero became the first interoperability protocol operating directly on Canton, enabling institutions to route tokenised assets across more than 165 public blockchains. The $CC token trades at a $5 billion fully diluted valuation.
None of that is the story. I’m going to talk about how Canton is now trying to shape what technology banks are allowed to use. And so far, it is the only one having that conversation.
The Argument Against ZK
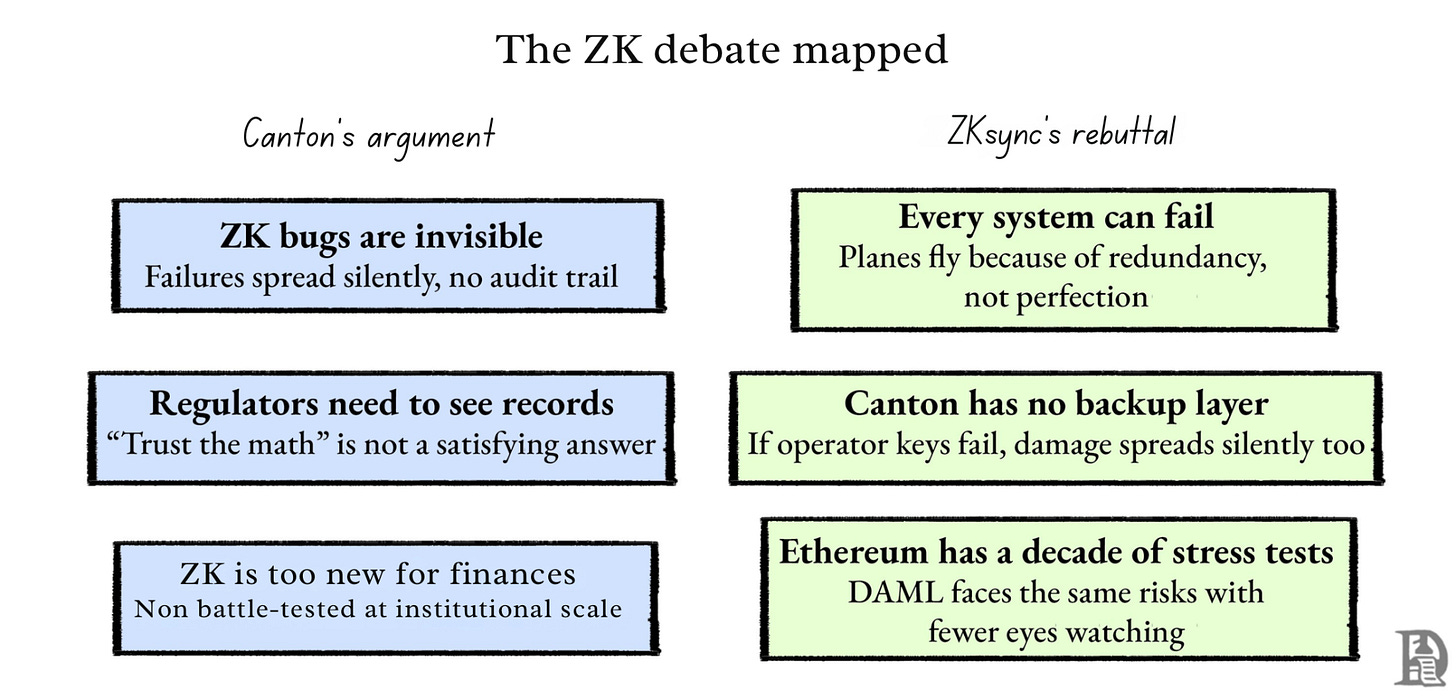
Canton’s case runs like this. ZKP bugs could go undetected because the underlying data stays private. A flaw that spreads silently, with no audit trail and no accountability, is kind of a dealbreaker.
They point to a real example. On April 16, 2025, Solana patched a zero-day vulnerability in its Confidential Transfers feature, which is powered by ZKPs. The bug could have allowed attackers to mint unlimited tokens. No one knows if it was ever exploited.
The person making this argument is Shaul Kfir, Canton’s co-founder and chief operations officer, who co-authored libsnark, a C++ library for creating zk-SNARK proofs. Is he dismissing a technology he does not understand? Highly unlikely.
His argument is that when a ZK proof fails, nobody sees it fail. The data stays private, the error stays hidden, and by the time anyone notices something is wrong, the damage has already spread. For a regulator whose job is to prove that a bank did not launder money, a system that says ‘trust the math’ is not a satisfying answer. They want to see the records.
And in Canton’s model, the only entities that can view those records in real time are the super validators, the same institutions whose keys, if compromised, are the single point of failure.
That argument does not have to be airtight to be effective. It just has to sound reasonable to someone who already does not fully trust crypto. To people who built their careers on paper trails and audit logs, the proof is invisible when it breaks hard. You do not need to win the technical debate, but you still need to make the other option feel risky.
Where It Breaks
ZKsync co-founder Alex Gluchowski answered publicly last week. Canton’s logic, he says, proves too much. If a technology can have bugs, and those bugs could be catastrophic, then we should never use it. By that reasoning,, we would have grounded every commercial flight in the 1970s and never built another plane. Fly-by-wire systems have bugs. Engine controllers have bugs. Autopilot software has failed in ways that have killed people. We did not stop flying. We built planes with multiple independent systems so that when one system fails, another catches it before the plane goes down.
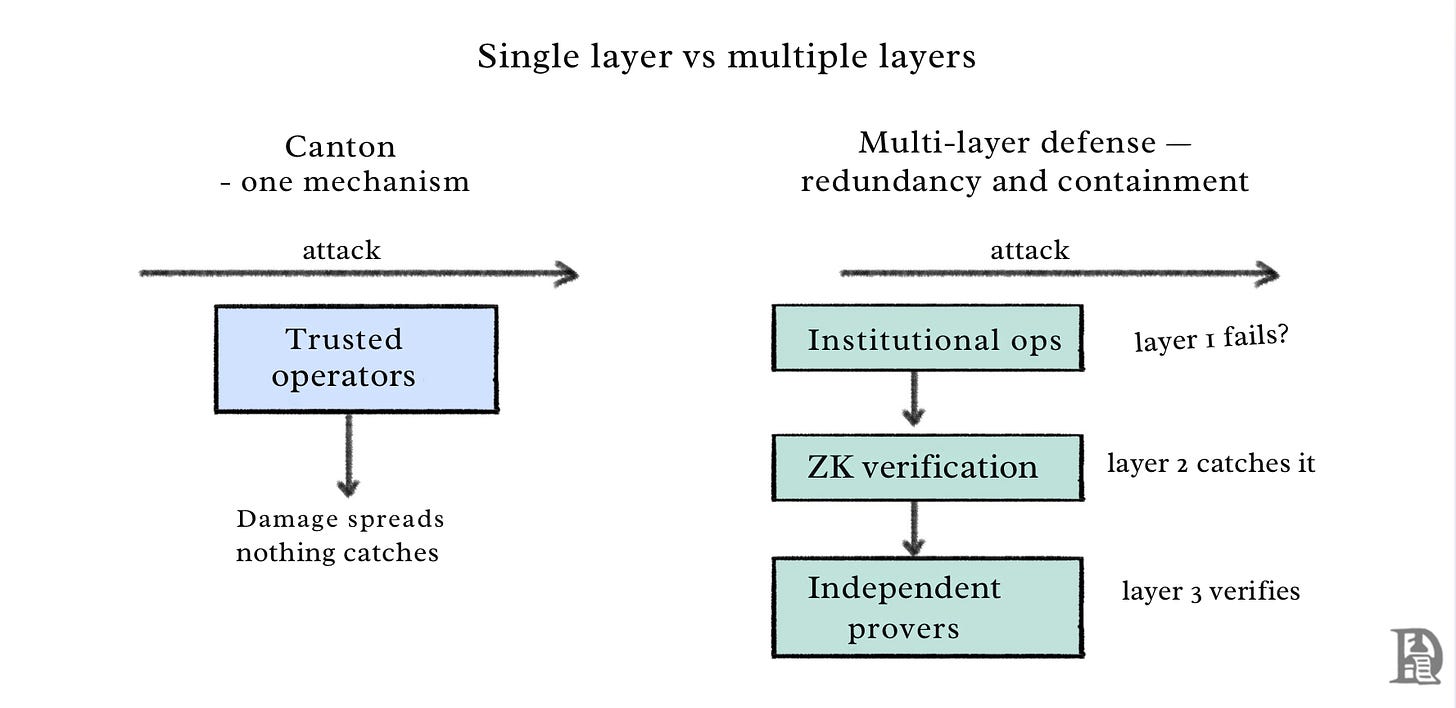
Is Canton answering what happens when an operator’s keys get compromised? There is no backup system or second layer checking the work. The trusted operator is the only line of defense. If that fails, the damage spreads silently through the network with nothing watching. By Canton’s own standard, that is the architecture that should worry regulators.
The solution to fallible technology has never been to find an infallible technology. It has been to build systems that expect failure and survive it anyway. A nuclear reactor does not stay safe because the software never breaks. It stays safe because when something breaks, five other things have to break simultaneously before anything catastrophic happens. Same with a pacemaker. Same with a commercial aircraft. The engineering principle is redundancy and containment. Build multiple independent layers so that when one fails, another catches it. And design the system so that when something does go wrong, the damage stays contained instead of spreading to everything connected to it.
Gluchowski applies the same test to Canton’s own architecture. Canton’s privacy and integrity model relies on a single mechanism, which is trusted operators segregating data between participants. There is no cryptographic verification layer or independent check. If operator keys are compromised, the manipulated state propagates silently across opaque chains of UTXOs with nothing watching. By Canton’s own logic (a single point of failure with catastrophic consequences), this is the architecture that should concern regulators.
The ZK bugs, Solana zero-day, all of these are real issues. But the response to fallible components is not to replace them with a different single point of failure dressed in institutional branding. The response is multiple independent lines of defense, blast radius limited by design, and the kind of adversarial stress testing that comes from a decade of open scrutiny. The EVM exists today as the product of continuous adversarial testing by the world’s most sophisticated actors, with hundreds of billions at stake, over more than a decade. Every maturity concern Canton raises about ZKPs applies to DAML, with a fraction of the mitigation available.
None of this settles the debate. But it reframes the debate. One approach to institutional risk management is arguing, in venues where regulation gets written, that it should be the only permitted approach.
There is something Canton’s argument leaves out entirely. ZK technology does not sit at a fixed risk level. It gets more secure as more people are allowed to verify. The core mechanic is a ZK proof lets someone prove a statement is true without revealing the underlying data. The verifier checks the proof, not the data. The more independent verifiers checking the same proof system, the harder it becomes for any bug or manipulation to go undetected. Nethermind formally verified the correctness of ZKsync’s on-chain ZK verifier using EasyCrypt in 2025, completing the first formal proof of this kind in a live zero-knowledge system. That is the adversarial scrutiny of an open system producing a demonstrably stronger result over time.
Canton’s model works in the opposite direction. Trust concentrated in a small set of approved operators does not compound in the same way. A closed system with approved verifiers has a ceiling on how much scrutiny it can absorb. The question of who is allowed to verify is not a footnote to the security debate. An open ZK system gets harder to compromise as the verifier network grows. A permissioned trust model stays as strong — and as vulnerable — as its weakest operator. A 2024 systematic analysis of known attacks found that approximately 96% of documented circuit-layer bugs in ZK systems were due to under-constrained circuits, a category of vulnerability that open adversarial testing is specifically designed to catch and eliminate. The bugs Canton points to are real. The open ecosystem is the mechanism for finding and patching them. Keeping that ecosystem closed does not make the bugs disappear. It just means fewer people are looking.
Canton stopped staying in its lane
Going back to the January piece I wrote, it positioned Canton as a parallel system. Solving a different problem for a different audience. Not competing with Ethereum for the same ground.
The LayerZero integration changes that positioning. It enables traditional financial institutions in Canton to route tokenised securities, digital bonds, and equities across more than 165 public blockchains, while maintaining compliance and confidentiality requirements. Investors can now use stablecoins on external public chains to fund primary purchases of Canton-based tokenised real-world assets. Canton-native tokenised instruments can move into other ecosystems for secondary market trading.
LayerZero Labs CEO Bryan Pellegrino says that “Canton has already built the rails for traditional finance, processing more than $350 billion in daily US Treasury repo volume. LayerZero’s job is to make sure those assets are available in every global market, across blockchains.”
This is Canton reaching into crypto’s liquidity pools, not remaining separate from them. Which creates a tension. Canton’s founders are in closed-door regulatory conversations, arguing that zero-knowledge proofs are too dangerous for institutional finance. At the same time, Canton-based assets are now flowing through LayerZero into a public blockchain ecosystem where ZK proofs underpin significant infrastructure. Including the products being positioned as the institutional alternative to Canton.
What that looks like in practice? A bank holds tokenised US Treasuries on Canton. Through LayerZero, those Treasuries can now move to Ethereum or Arbitrum, where they can be posted as collateral in Aave, borrowed against on Ondo, or used as a base asset in DeFi lending protocols. The instrument stays institutional-grade and compliant on Canton’s rails. The liquidity it accesses is crypto-native. Ondo Finance is already doing a version of this with LayerZero. Its tokenized Treasury product USDY operates across four blockchains with $700 million in TVL, usable as collateral across DeFi. Canton now has a direct path into that same ecosystem. The bank gets the yield and the composability. DeFi gets the institutional collateral. And Canton gets to argue to regulators that ZK proofs are too dangerous, while its assets flow freely through chains that run on them.
Using crypto’s infrastructure while arguing to regulators that crypto’s foundational privacy technology is a systemic threat is a coherent strategy if the goal is regulatory capture. It is not incoherent. You can say out loud, because the ZK camp has not yet organised a response at the same level.
The ZK camp’s most visible contribution to the regulatory conversation, as of this week, is Gluchowski’s thread. It is a good thread. Canton has lawyers in those meetings. Goldman’s relationships. A decade of work building trust with regulators whose sign-off determines what a systemically important bank can run.
What Is At Stake For ETH
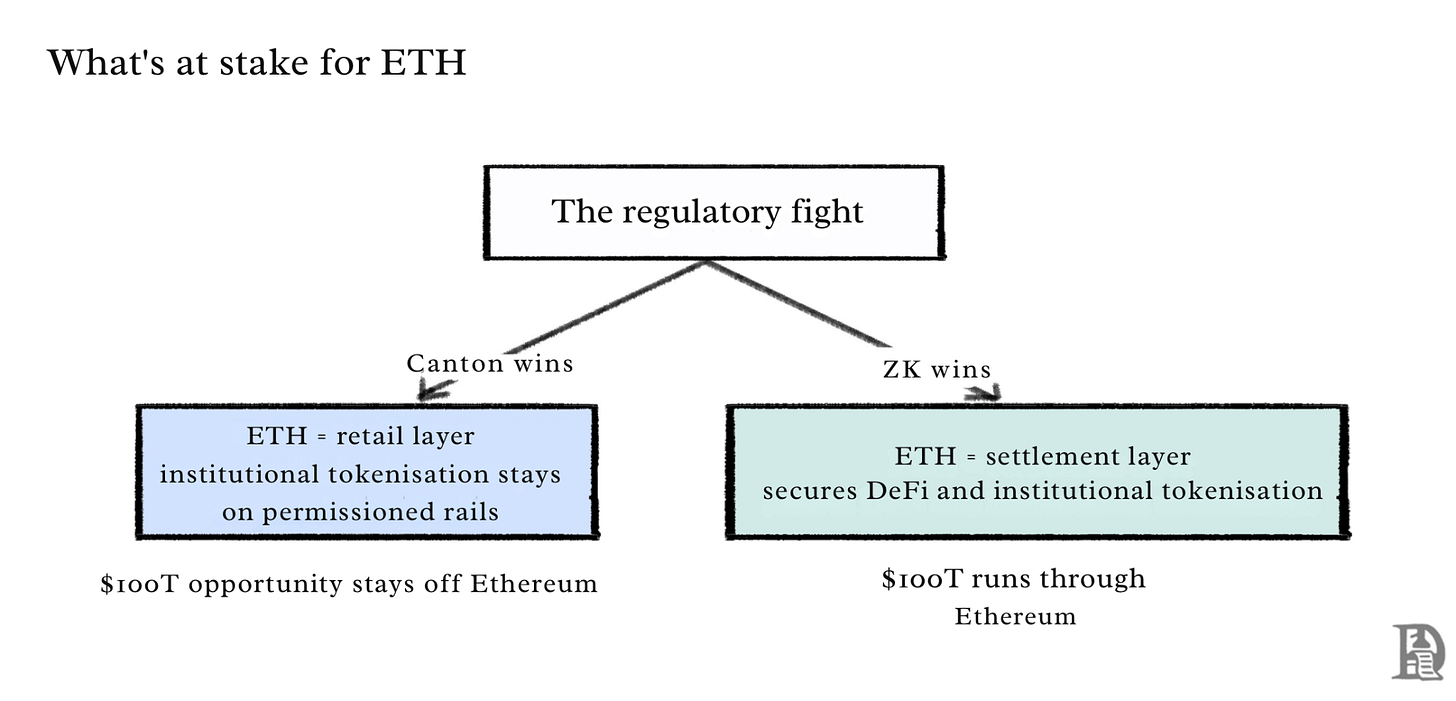
This is not abstract for anyone holding ETH or watching where institutional tokenisation lands.
If Canton wins the regulatory argument, which is if ZK proofs get categorised as too risky, too opaque, too novel for the frameworks that govern systemically important institutions, then Ethereum’s path to institutional settlement gets closed before it fully opens. The $100 trillion tokenisation opportunity that Larry Fink wrote about in his annual letter stays on permissioned rails. Ethereum settles DeFi. That is not nothing. But it is not the settlement layer for global finance.
If the ZK camp wins, which means if zkSync’s Prividium and emerging institutional-grade ZK infrastructure earn regulatory approval alongside or ahead of Canton’s model, then the calculus shifts majorly. The chain that secures DeFi starts securing institutional tokenisation. ETH’s position in the financial stack expands. The asset that seemed like it might be getting sidelined by the institutional layer ends up being the foundation of it.
Visa just joined Canton as a super validator. DTCC is moving toward production. Broadridge is already processing hundreds of billions in daily volume on Canton rails. Testing participants include Goldman Sachs, BNP Paribas, Tradeweb, and Citadel Securities. The institutional flywheel is moving and has been for long enough to have real momentum.
In January, I said that Canton is not trying to replace Ethereum. That is still true. The goal is narrower and more effective than replacement. The goal is to ensure Ethereum never gets the chance to compete in the same market. Not by building better. By certifying first. By getting to the regulator before the regulator gets to the technology and forming the frame through which everything that comes after gets evaluated.
Crypto has always competed on visible metrics, such as TVL, fees, users, transactions, and token price. Canton never competed on any of those. It is based on trust, which is invisible, accumulates slowly, and is almost impossible to replicate once someone else has it.
The funny thing is that ZK proofs were invented to solve exactly the problem Canton is exploiting. You should not have to trust anyone if the math can prove the thing without showing you the thing. Canton’s argument is that the math cannot be trusted either. So trust the institution instead. The one whose risks got named last wins.
Token Dispatch is a daily crypto newsletter handpicked and crafted with love by human bots. If you want to reach out to 200,000+ subscriber community of the Token Dispatch, you can explore the partnership opportunities with us 🙌
📩 Fill out this form to submit your details and book a meeting with us directly.
Disclaimer: This newsletter contains analysis and opinions of the author. Content is for informational purposes only, not financial advice. Trading crypto involves substantial risk - your capital is at risk. Do your own research.






This is one of those moments where the real battle isn’t happening on the chart, it’s happening in the frame through which the chart will eventually be interpreted .
What Canton is doing isn’t competing on performance or users. It’s competing on legitimacy. If you can define what is considered “safe” before the market even has a chance to choose, you don’t need to win on merit, you just need to win on permission.
Markets have seen this before. Railroads, telecom, banking. The winners weren’t always the best technology, they were the ones that got written into the rules.
That’s why this matters more than it looks. If the narrative around risk gets anchored early, it shapes where capital is allowed to flow, not just where it wants to go.
And once that framework is set, the market tends to follow it, even if the underlying reality takes longer to catch up.